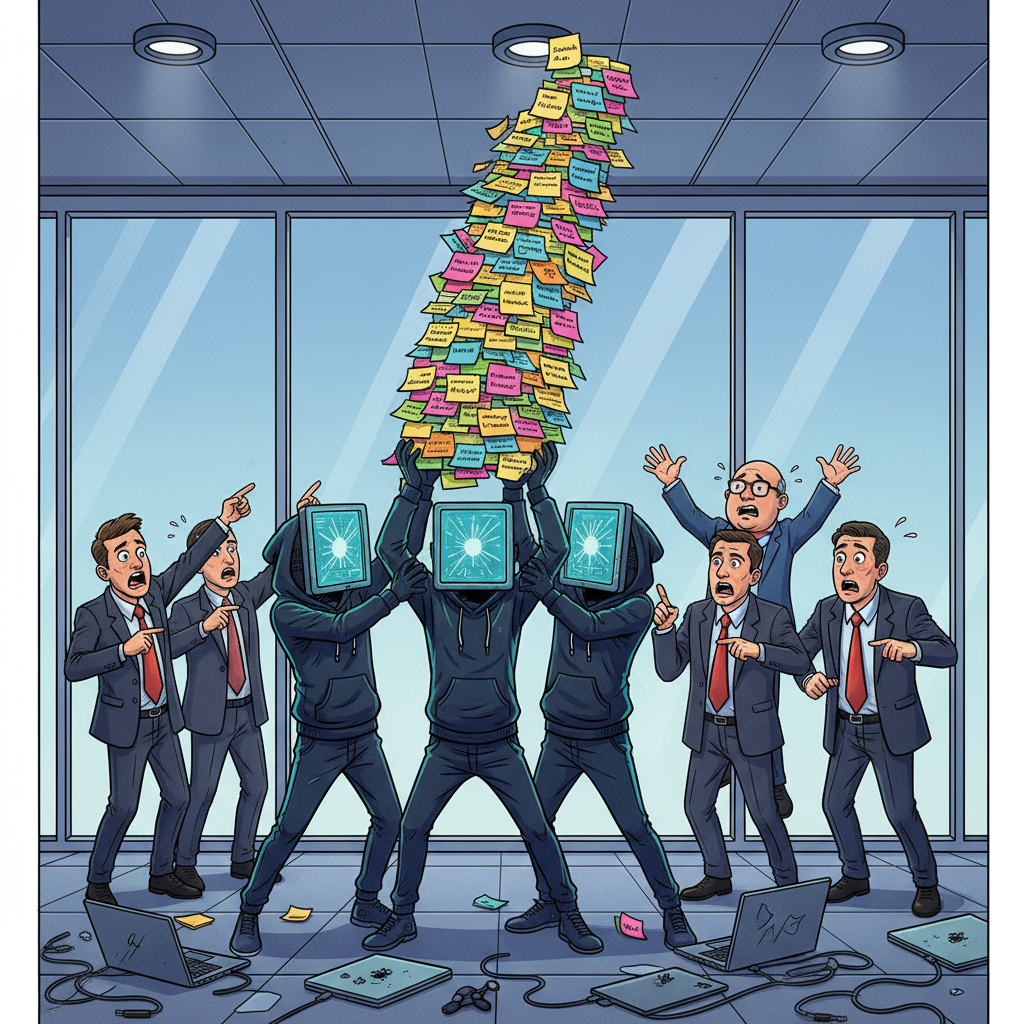
WASHINGTON D.C. — The notorious hacking collective known as 'Salt Typhoon' has claimed responsibility for a new wave of breaches across major tech and telecommunications companies, revealing that their sophisticated methods largely involved finding passwords scrawled on sticky notes affixed to monitors.
“We’ve invested heavily in advanced persistent threats, zero-day exploits, and state-of-the-art phishing campaigns,” stated a spokesperson for the group, operating under the alias 'Binary Bandit,' in an encrypted message. “But frankly, the easiest path to sensitive data has consistently been the yellow square stuck right next to the webcam. It’s almost insulting.”
Industry analysts expressed a mixture of concern and resignation. Dr. Evelyn Reed, head of digital forensics at the Institute for Cybernetic Absurdity, noted, “For years, we’ve preached multifactor authentication, complex character strings, and regular password changes. It appears the human element, specifically the ‘I’ll just write it down for a second and then remember it’ element, remains the weakest link.”
Salt Typhoon’s latest exploits reportedly granted them access to millions of user accounts, corporate networks, and even a few highly secure government databases. When asked about the specific techniques used, 'Binary Bandit' added, “Sometimes they’re under the keyboard. Sometimes they’re taped to the wall. Honestly, we just walk around until we see one. It’s less ‘hacking’ and more ‘observational scavenging.’”
Sources close to the investigation confirm that several breached companies are now considering mandatory 'clean desk' policies that specifically forbid analog memory aids within 100 feet of a computer terminal.