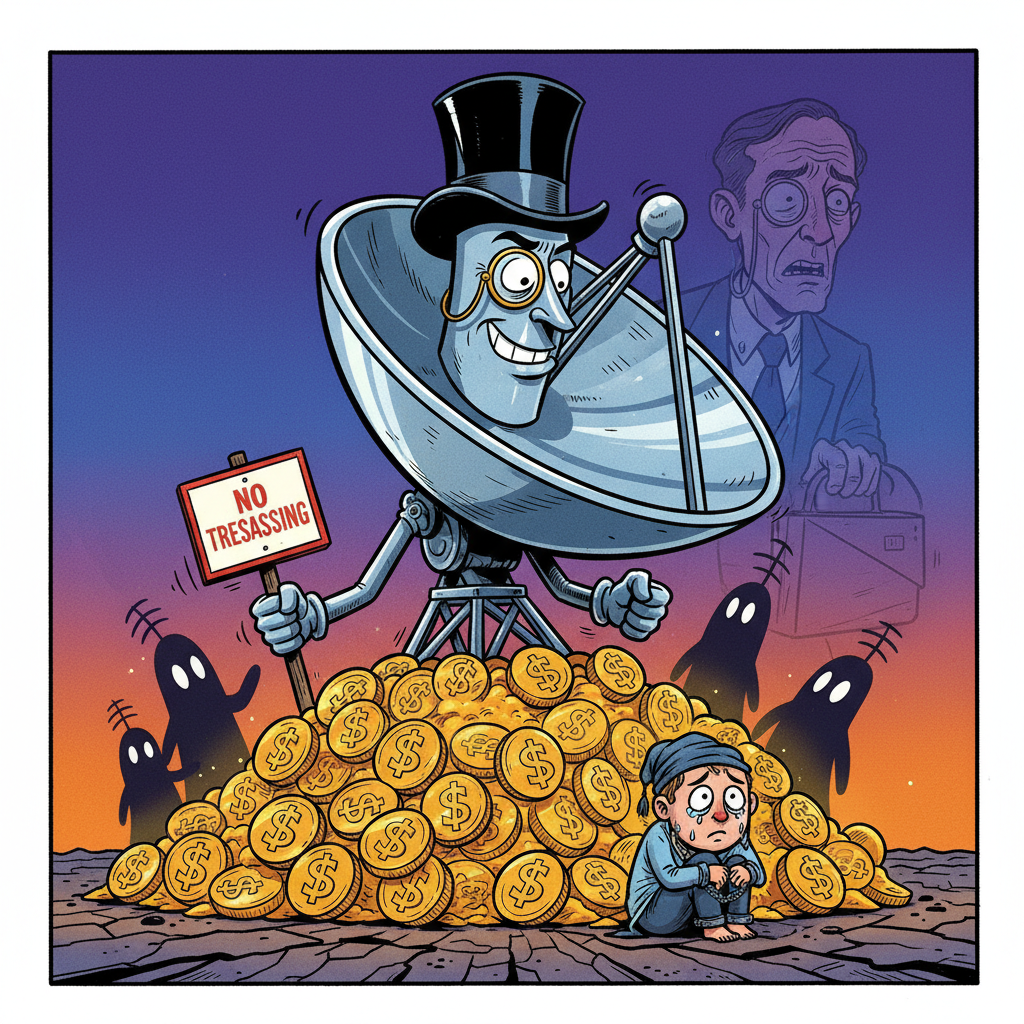
CANBERRA, ACT – Australian hospitals are reportedly on high alert after a recent cyberattack on medical technology giant Stryker, with officials confirming that Iranian-backed hackers successfully installed a suite of non-essential software and a mandatory 'StrykerCare+' subscription service across all connected devices.
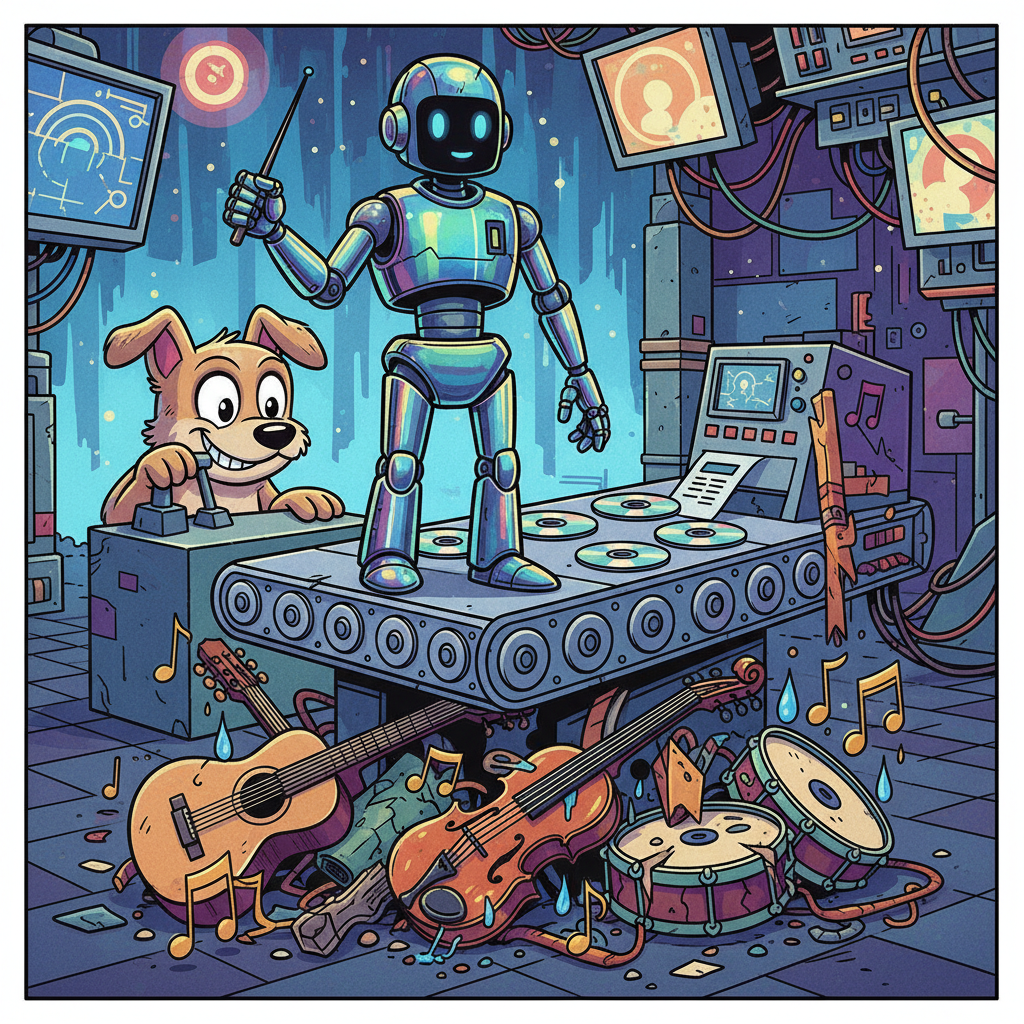
The breach, which targeted Stryker's global network, has left critical hospital equipment, from MRI machines to defibrillators, running slower than usual and occasionally displaying full-screen advertisements for 'enhanced diagnostic algorithms' and 'platinum patient comfort packages.'
“We’re confident patient data remains secure, but we can’t say the same for their patience,” stated Dr. Evelyn Reed, head of IT at Royal Melbourne Hospital. “Every time a surgeon tries to adjust a robotic arm, they’re prompted to ‘upgrade to Stryker Pro for 20% faster response times.’ It’s like trying to defuse a bomb while battling a Windows update.”
A spokesperson for Stryker, who wished to remain anonymous to avoid being associated with the company’s recent 'innovations,' assured the public that the new software includes “robust security patches and a delightful new startup jingle.” They added, “We believe this incident has actually provided an invaluable opportunity to introduce our cutting-edge monetization strategies directly into the healthcare workflow.”
Industry experts suggest the hackers may have simply outsourced their attack to Stryker’s own marketing department, noting the striking similarity between the 'malware' and typical corporate software updates. Hospitals are now reportedly considering a class-action lawsuit, not against the hackers, but against Stryker for the forced installation of 'unskippable pre-op video ads.'
Patients are advised to bring their own ad-blockers to all future medical appointments.